
Face The Fight
Learn how USAA is responding to make a difference so that those who have defended our freedom have the resources they need to win the fight against veteran suicide.

Corporate Responsibility
We serve military families and strengthen local communities through philanthropic grantmaking, employee giving and volunteer work.

Our Operating Companies
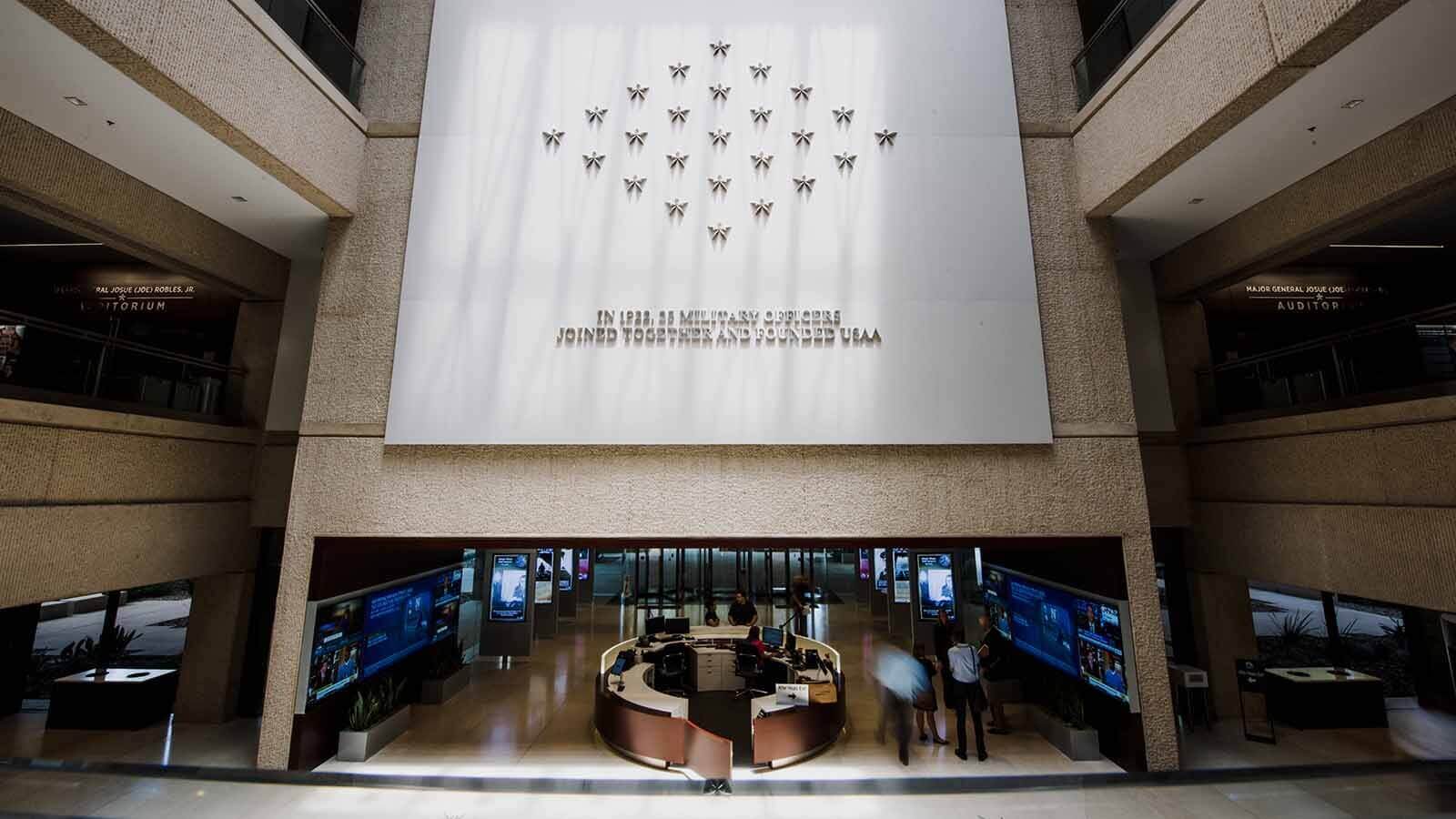
USAA is among the leading providers of insurance, banking, investment and retirement solutions to members of the U.S. military, veterans who have honorably served and their families.
USAA Leadership Team
Strong leadership is key to fulfilling our mission. Meet the people who lead us in going above for those who have gone beyond.
Latest news

USAA Advocates for Safe Driving Habits During 100 Deadliest Days of Summer for Teens
New Safe Driving Simulator virtual experience helps drivers identify bad habits ahead of summer travels

USAA’s Poppy Wall of Honor® Returns to National Mall for Sixth Year to Honor and Remember Fallen Service Members
Enhanced experience provides immersive storytelling to illustrate all that was given in service to our country

USAA Appoints Brian Goldman as Chief Risk Officer
USAA announced today the appointment of Brian Goldman as its new Chief Risk Officer, effective May 27.




